This article goal is to explain how to set-up an HTTPS configuration with Mutual Authentication (two way SSL) in BusinessWorks.
The article will cover both the BusinessWorks Server implementation and BusinessWorks Client implementation.
Overall architecture
The following diagram is showing the server and client components and their relative keystore and truststore files with their contents.
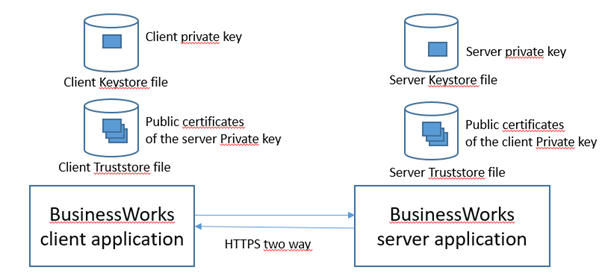
Note that the above solution can be simplified by using on both sides (server and client) a single Keystore file to hold the private key and the public certificates.

### Server Implementation
Pre-requisites
To set-up a server HTTPS configuration with Mutual Authentication you need the following elements:
. The server private key stored in a Keystore file
. The Keystore file password
. The private key alias
. The private key password
. The client public certificates stored in a Truststore file
. The Truststore file password
Example of a Keystore file containing a private key seen in the Key Explorer tool :

On the screen shot above you can see the private key alias that is ‘myservice’.
The private key includes the related public keys.

Details on the Private Key showing the related Public certificates (two certificates in this example)
Set-up of the BusinessWorks configuration
Assuming that the configuration to expose the REST API or the Service in plain HTTP is already set-up the following actions need to be completed to change the configuration to HTTPS with Mutual authentication:
#1 in the HTTP Connector resource check the Confidentiality option

#2 Click on the button to select or create an SSL Server Configuration

#3 Click on Create shared resource (or select an existing resource)

#4 Enter a name for the new SSL Server resource and click Finish (if creating a new resource)

If you create a new resource you can select to use the suggested name or enter a new one.
#5 In the SSL Server Resource click the button to select or create an Identity Store Provider (pointing to the Server KeyStore file)

#6 Click on Create Shared Resource (or select an existing resource)

If you create a new resource you can select to use the suggested name or enter a new one.
#7 Configure the Key Store provider (pointing to the Server KeyStore file)
Select the Provider (SUN is the default value when nothing is selected), enter the path to the server KeyStore file and the server KeyStore file password (these values should be managed using properties). You may also need to adjust the Keystore type.
Note that by default BusinessWorks is trying to refresh KeyStore files every hours, this allows a KeyStore to be updated without downtime (this is useful to manage Certificates expiry).

# 8 Enable Mutual Authentication and create a KeyStore provider for the TrustStore (pointing to the server TrustStore file)
Check the ‘Enable Mutual Authentication’ option and set ‘Client Auth Type’ to ‘required’.
Important note : setting ‘Client Auth Type’ to ‘optional’ is only valid for testing purpose while with this set-up the client public certificates are not verified by the server (which means Mutual Authentication is not enforced).
Then click the button to select or create a Trust Store Provider.

#9 Click on Create Shared Resource (or select an existing resource)

If you create a new resource you can select to use the suggested name or enter a new one.
#10 Configure the KeyStore provider for the Trust Store (pointing to the server TrustStore file)
Select the Provider (SUN is the default value when nothing is selected), enter the path to the server TrustStore file and the server TrustStore file password (these values should be managed using properties). You may also need to adjust the Keystore type.
Note that by default BusinessWorks is trying to refresh KeyStore files every hour, this allows a KeyStore to be updated without downtime (which is useful to manage Certificates expiry).

# 11 Complete the configuration of the SSL Server resource
Enter the Key Alias name and Key password (these values should be managed using properties).

Note : depending on the security requirements you have to manage you may need to adjust the values of some of the parameters present in the ‘Advanced SSL Server Configuration’ section.
#12 Save your project and check the configuration
The HTTP connector resource should look like this :

The SSL Server resource Configuration should look like this:

The configuration of the KeyStore provider resource for the server KeyStore should look like this:

The configuration of the KeyStore Provider resource for the server Truststore should look like this :

### Client implementation
Pre-requisites
To set-up a client HTTPS configuration with Mutual Authentication you need the following elements:
. The client private key stored in a Keystore file
. The Keystore file password
. The private key alias
. The private key password
. The server public certificates stored in a Truststore file
. The Truststore file password
Set-up of the BusinessWorks configuration
Assuming that the configuration to call the REST API or the Service in plain HTTP is already set-up the following actions need to be completed to change the configuration to HTTPS with Mutual authentication:
#1 In the HTTP Client resource check the Confidentiality option

#2 Click on the button to select or create an SSL Client Configuration

#3 Click on Create shared resource (or select an existing resource)

#4 Enter a name for the new SSL Client resource and click Finish (if creating a new resource)

If you create a new resource you can select to use the suggested name or enter a new one.
#5 In the SSL Client Resource click the button to select or create a Key Store Provider for the client TrustStore (pointing to the Client TrustStore file)

#6 Click on Create Shared Resource (or select an existing resource)


If you create a new resource you can select to use the suggested name or enter a new one.
#7 Configure the KeyStore provider for the client TrustStore (pointing to the Client TrustStore file)
Select the Provider (SUN is the default value when nothing is selected), enter the path to the client TrustStore file and the client TrustStore file password (these values should be managed using properties). You may also need to adjust the Keystore type.
Note that by default BusinessWorks is trying to refresh KeyStore files every hours, this allows a KeyStore to be updated without downtime (this is useful to manage Certificates expiry).

# 8 Enable Mutual Authentication and create an Identity Store provider (pointing to the Client KeyStore file)
Check the ‘Enable Mutual Authentication’ option.
Then click the button to select or create a Identity Store Provider.

#9 Click on Create Shared Resource (or select an existing resource)

If you create a new resource you can select to use the suggested name or enter a new one.
#10 Configure the Identity Store provider (pointing to the Client KeyStore file)
Select the Provider (SUN is the default value when nothing is selected), enter the path to the client KeyStore file and the client KeyStore file password (these values should be managed using properties). You may also need to adjust the Keystore type.
Note that by default BusinessWorks is trying to refresh KeyStore files every hours, this allows a KeyStore to be updated without downtime (this is useful to manage Certificates expiry).

# 11 Complete the configuration of the SSL Client resource
Enter the Key Alias name and Key password (these values should be managed using properties).

Note : depending on the security requirements you have to manage you may need to adjust the values of some of the parameters present in the ‘Advanced SSL Client Configuration’ section.
#12 Save your project and check the configuration
The HTTP client resource should look like this :

The SSL Client resource Configuration should look like this:

The configuration of the KeyStore provider resource for the client KeyStore should look like this:

The configuration of the KeyStore provider resource for the client TrustStore should look like this:

Useful elements
To write this article I used a set of sample Keystore files available at the following URL (download the x.509-sample-keys-and-certificates.zip file):
https://www.swview.org/blog/sample-x509-certificate-collection-publicprivate-keys-java
Article explaining how to access a REST API or a Service exposed over HTTPS using one way SSL :
https://community.tibco.com/articles/tibco-activematrix-businessworks/bw6x-bwce-security-how-to-configure-an-http-client-connection-to-access-a-rest-api-or-web-services-exposed-over-https-in-businessworks-6x-and-businessworks-container-edition-r3387/
Article explaining how to expose a REST API or a Service exposed over HTTPS using one way SSL :
https://community.tibco.com/articles/tibco-activematrix-businessworks/bw6x-bwce-security-how-to-expose-an-api-or-a-service-in-https-in-businessworks-and-businessworks-container-edition-r3397/
Article explaining how to debug SSL / TLS configuration in BusinessWorks :
https://community.tibco.com/articles/tibco-activematrix-businessworks/bw6x-bwce-how-to-debug-ssltls-connections-in-businessworks-and-businessworks-container-edition-r3392/
Additional elements
You can also refer to the attached sample project



Recommended Comments
There are no comments to display.
Create an account or sign in to comment
You need to be a member in order to leave a comment
Create an account
Sign up for a new account in our community. It's easy!
Register a new accountSign in
Already have an account? Sign in here.
Sign In Now